Artificial intelligence ensures a more defensive cyber security on the Internet of Things
Artificial intelligence (AI) can be a very useful tool to learn the behaviors of cyber-attacks, and responds to them with appropriate actions, writes Guru Prasad Bhandari.
KNOWLEDGE @ KRISTIANIA: Cyber security
Nowadays, the standard of the organizations and countries are measured by how secure they are in terms of power and services. From agriculture to aviation, and manufacturing to finance, security is considered as a key for benchmarking the product and services.
The term Internet of Things, or IoT, refers to the collective network of connected hardware devices, software and communication technology. As an example, the IoT can be used to create a smart home with WiFi enabled appliances all connect to the internet and share the data that can be control remotely from your cell phone.
However, the incremental record of cyberattacks threatens . Attackers hack others’ infrastructure often to warn people or earn money, or sometimes just for hobbies of breaking the embedded systems.
Read also
Cyber security through artificial intelligence
For establishing security and safety, in addition to the normal precautions such as a firewall and antivirus software, artificial intelligence (AI) can be a very useful tool to learn the behaviors of these cyber-attacks and responds to them with appropriate actions.
By 2025, cybercrime is expected to cost the global economy $10.5 trillion a year which is more than $3.3 million per second.
Smart environments with AI are more secure from planning to development and deployment of software sufficiently reflecting the diverse cyberattack scenarios. We at Kristiania University College, work through the ENViSEC project to build AI-enabled method for cybersecurity towards secure smart environments.
Immense costs for the global economy
Cyberattacks refer to any form of malicious activities that target IT systems to gain unauthorized access to the information. By 2025, cybercrime is expected to cost the global economy $10.5 trillion a year which is more than $3.3 million per second. Recently in July 2021, even for a single cyberattack, Saudi Aramco faced $50 million ransom in cyber extortion over leaked data .
Moreover, the AI market in cybersecurity is expected to significantly grow at a compound annual growth rate of 24.2 per cent from 2020 to 2029 to reach $66.22 billion by 2027. Therefore, the AI can be inspected as a next generation tool to mitigate cybersecurity attacks and reinforce the best practices for improved and secure IT systems.
AI enables effective cyber security
Cybersecurity crossponds with the set of IT setup and processes configured to protect digital devices, computers, programs and data from attack, unauthorized access, change, or destruction .
Inspired by the human brain, Artificial Intelligence (AI) enables the machine to think, learn, act, and react in a similar fashion we human beings do. AI can automate many security tasks of IT systems that a human often does manually. AI-enabled security of technological environment involves multiple levels of intelligent strategies at various stages of the embedded software development process from planning to deployment.
Every device connected to the network through any medium should be secured before and while connecting to the network.
For that, a significant number of AI-enabled security applications such as automated malware attacks detection, data loss prevention, intrusion detection/prevention, threat intelligence, fraud detection, anomaly detection, source code vulnerability prediction, automatic program repair, patch prediction enables effective cybersecurity.

Read also (In Norwegian)
Ensures a more defensive system
Every device connected to the network through any medium should therefore be secured configuring with security in mind before and while connecting to the network. Each IoT device can individually perform different behavior in the network and the way handling its anomalous behavior needs specific strategy.
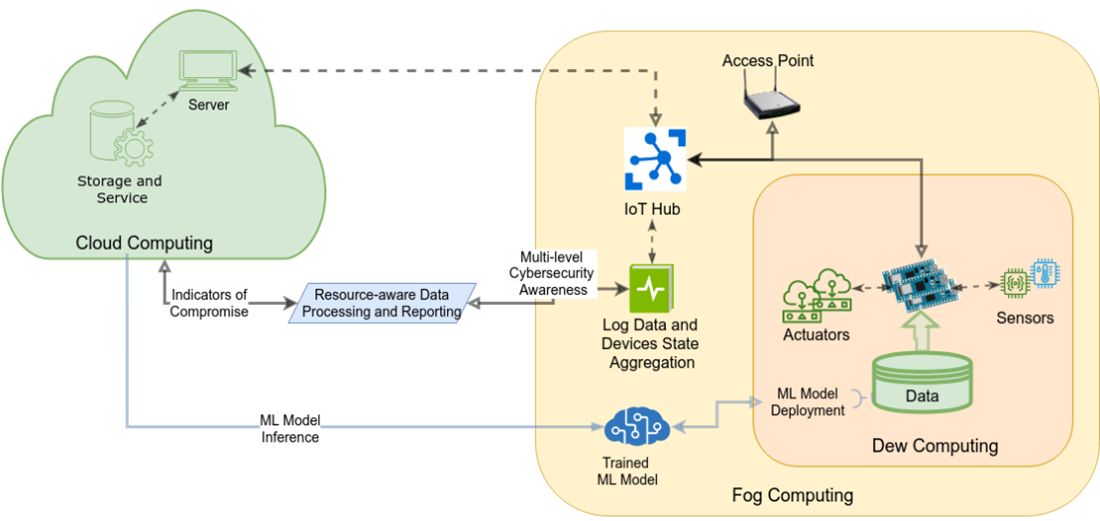
For that, a device-oriented lightweight AI model to predict the malfunction of the device, ensures a more defensive system. Figure 1 shows the AI-enabled framework for cybersecurity in smart environments with cloud computing support.
Benefits of embedded-AI
Some of the notable advantages of embedded AI software models to smart environments are;
- Security and privacy: The inference processing of the data and construction AI models in cloud computing needs to transfer the data and the predictive model in the cloud. Hence, that can encounter the security and privacy issues being the data available in the cloud. Data and the model relying on systems on chips (SoCs) ensures that security and privacy of the local data and AI software.
- Reduced dependence on the cloud: The inference processing of the data and AI models are heavily dependent on cloud or high-performance computing. If IoT devices and chips can construct the AI models, then the dependence on cloud can be significantly reduced by low power devices and chips .
- Improved products and services: Embedding the AI models on SoCs and IoTs optimizes the chip’s architecture thereby reducing instruction counts, energy consumption, and computation time. The embed-AI models can result in improved the overall products and services, increased operational efficiency, and enhanced security and risk management with predictive maintenance for equipment.
Challenges on developing AI software models for embedded devices
On-device-AI ensures security and privacy concerns on sensitive data that remains unexposed to the public internet. It also reduces the dependency on cloud computing for inference processing. However, enabling AI models on these tiny embedded devices does not remain without challenges. Some of the major challenges are as follows:
- Resource-constraints environments: The tiny IoT devices often consist of limited processing power, memory, and energy capacity. Due to its resource limitations, middleware developers must either compromise with CIA (confidentiality, integrity, and availability) or put complex low prioritized computations to off-chip and keep only necessary ones on-chip.
- Data variances: AI-enabled model for cyberattacks prediction needs significant data gathered from diverged scenarios of the environments to train the machine learning model. So that the trained model in the future can be utilized to detect malware attacks occurred in the systems. However, the major problem in the field of AI-enabled cyberattacks prediction is lacking ground truth data of attacks sample. To deal with the shortcomings, a considerable number of researchers and practitioners have manually curated the data in their specific environment artificially injecting the attacks to represent the malware attacks patterns and behaviors.
- Data imbalance: The existing available data may also suffer from the data imbalance problem not having the proportion of the data that distinguish one attack from other attack group which introduces problem with generalization. Off course originally diversed and generalized data or by tuning it, promotes more robust and reliable AI model with more accurate and precise data.
- Inference Processing: The training process of the AI models may require intensive resources which may need powerful computers than these IoT devices. However, once the model is constructed, deploying it onto a device to process the incoming data in terms of signals, images, audio and video to look for and recognize it based on the trained model can be done.
References:
CNBC (2021). https://www.cnbc.com/2021/07/22/saudi-aramco-facing-50m-cyber-extortion-over-leaked-data.html.
Buczak, A. L., & Guven, E. (2015). A survey of data mining and machine learning methods for cyber security intrusion detection. IEEE Communications surveys & tutorials, 18(2), 1153-1176.
Shalaginov, A., & Grønli, T. M. (2021). Securing Smart Future: Cyber Threats and Intelligent Means to Respond. In 2021 IEEE International Conference on Big Data (Big Data) (pp. 2560-2564). IEEE.
Meticulous Research (2020). https://www.meticulousresearch.com/product/artificial-intelligence-in-cybersecurity-market-5101.
Peterson, Z. (2020). The Future of Embedded AI and Custom SoCs, https://www.nwengineeringllc.com/article/the-future-of-embedded-ai-and-custom-socs.php.
ENViSEC, (2021). ENViSEC: Artificial Intelligence-enabled Cybersecurity for Future Smart Environments. https://smartseclab.com/envisec/.
Ahmed, E., Yaqoob, I., Gani, A., Imran, M. and Guizani, M., (2016). Internet-of-things-based smart environments: state of the art, taxonomy, and open research challenges. IEEE Wireless Communications, 23(5), pp.10-16.
The ENViSEC project towards cybersecurity
The ENVISEC project is for establishing AI-enabled cybersecurity to make secure and reliable smart systems. We focus on building malware and attacks detection models to different layers of the multi-agent systems. Our new method contributes to the prediction of security issues in the initial stages of the system lifecycle that contributes towards a resource-efficient environment.
Text: Guru Prasad Bhandari, Software Engineer at the School of Economics, Innovation and Technology, Kristiania University College
We love hearing from you:
Send your comments and questions regarding this article by E-mail to kunnskap@kristiania.no.
N

How blockchain technology can enhance trust in social business
Blockchain technology can be applied to enhance transparency and accountability in social business operations and thus lead to trust.Les mer
Predicting your next move
We can address societal challenges and gain valuable business insights by predicting people's next move.Les mer
N2

What if your work was automated?
Oganizations can successfully develop automation initiatives and facilitate meaningful work by involving their employees in the process.Les mer
Hva skal intelligente roboter gjøre med uetiske mennesker?
Intelligente roboter vil i økende grad kunne reflektere over etikk. Det hevder professor Jon Arild Johannessen i en fersk bok.Les mer



